Ransomware, SAP E-Recruiting, and Why HR is Under Cyberattack
Jun 7, '18 by Joerg Schneider-Simon
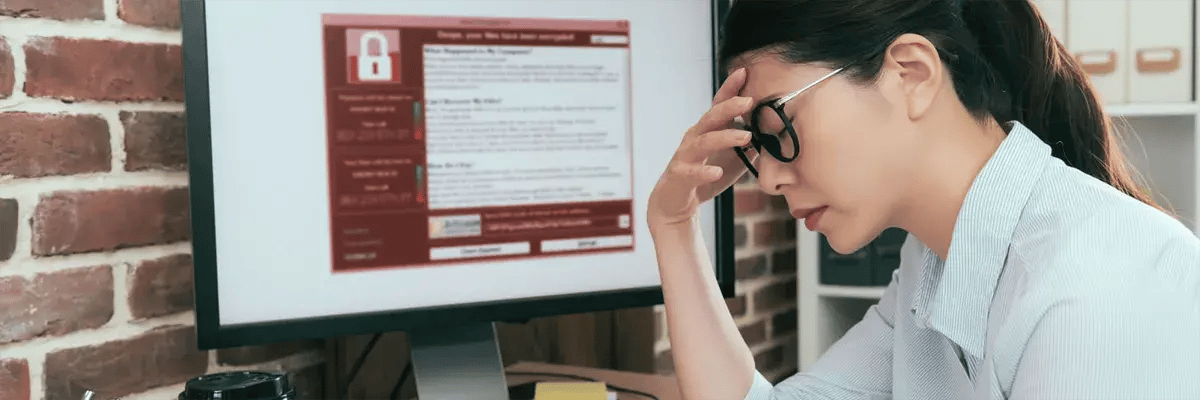
Cybercriminals are always looking for ways to get through a company’s cybersecurity defenses. And in 2017, Human Resources departments became a prominent victim.
A Petya ransomware variant named “GoldenEye” targeted HR departments, by way of seemingly-innocuous job applications. Once launched, it encrypted users’ files before presenting them with a ransom note.
GoldenEye might be the most famous attack on HR departments, but it certainly won’t be the last. And HR departments using SAP E-Recruiting are no less vulnerable.
How HR Departments Were Targeted
The nature of HR departments makes them enticing prey. According to Check Point security researchers, GoldenEye ransomware targeted firms' HR "due to the fact they usually cannot avoid opening emails and attachments from strangers, a common malware infection method".
With GoldenEye, the tactic was to lull HR into a false sense of security.
An email would arrive with a brief message from a fake job applicant. The first attachment in the email would be a perfectly clean, malware-free, legitimate-looking cover letter. The second file would be an Excel file posing as a job application — which contained malicious macros. A “Loading…” screen requested users to enable content, at which point the macros would run, locking the victims out of accessing their own files, and often their computer.
The odd part of this was that the ransom was not a large amount: about $300 per hijacked computer.
This led cybersecurity experts to believe that the goal was not money, but instead, something more nefarious: the destruction of data, with the aim of crippling — or even bringing down — the company.
Since the GoldenEye attack, many companies have been on increased alert for cyberattack via fake job applications and have ensured that their anti-virus programs scan all attachments that come in via their email server.
That’s all well and good, but … what if job applications don’t come in via email?
Ransomware and SAP E-Recruiting
Many companies use SAP to streamline their data and processes, with SAP E-Recruiting being a popular choice for managing processes like finding new employees, promoting their professional development, and retaining them for the long term.
The appeal of SAP E-Recruiting is also in its automation. Companies can easily integrate a job application form onto their Careers page where applicants can fill out their details and attach a resume. From there, it manages their talent pool with functions like electronic screening, filtering, sorting, ranking, and more, saving HR professionals time and labor.
However, because E-Recruiting, by its very nature, receives input and files from the outside world, it is vulnerable to cyberattack. And because E-Recruiting is so often integrated with other applications like ERP, any attacks that come through E-Recruiting can swiftly spread throughout the entire SAP system.
At bowbridge, we wanted to know just how vulnerable most E-Recruiting installations were to cyberattack, so we performed some tests on 120 randomly selected installations. Among our findings:
- 30% of the portals did not implement any filtering or restrictions whatsoever on the types of files accepted by the application
- 87% of the implementations we tested allowed uploading of Office documents with macros (which is what GoldenEye used to deliver its ransomware) in the old format (CDF, pre- Office 2007) and 33% allowed uploading of documents with macros in the new format (OOXML).
- 89% of portals we tested allowed PDF with embedded code to launch external applications.
How Companies Can Protect Themselves
Obviously, the answer isn’t to go back to snail mail. Large organizations still need the automated ease that E-Recruiting brings. So, how can they keep their E-Recruiting application from being a portal for cyberattacks?
Here are a few best practices:
- Ensure that SSL encryption is the default for all E-Recruiting-related links, and that this encryption cannot be bypassed.
- Implement two-step authentication for new accounts and require the creation of strong passwords.
- Ensure that SAP security patches are installed immediately upon release.
- Set SAP filters to only allow in the file types that are commonly used for job applications.
Even with these best practices, however, there are still vulnerabilities. One example is with file types. SAP filters can be set to use MIME types to block out Excel files, for example. But SAP’s filters simply map the extension name to a MIME type. So, someone could very easily slip an Excel file past SAP’s filters simply by changing the extension to .docx, for example.
In addition, attachments that are uploaded via SAP do not undergo screening by typical anti-virus programs, either through on-demand scans or scheduled scans.
Therefore, in addition to the best practices listed above, the best way to keep malware-laden files from penetrating an SAP system is to implement a strong anti-virus solution that is made specifically for SAP. A comprehensive solution can scan any uploaded files to ensure that the MIME type matches the actual content of the file, that no active content is contained within, and that there is no malware lurking within.
Finding the right candidate can be tricky enough. By setting up strong defenses, organizations can ensure that their HR professionals can focus on what they do best, without being derailed by cyberattack.

Share this on social: